
AI Strikes Back: Using an LLM to write COBOL
When AI-powered coding meets punch-card era technology


When AI-powered coding meets punch-card era technology

The Model Context Protocol promises seamless AI integration, but are we opening security holes? I explore common MCP vulnerabilities and how to detect them.
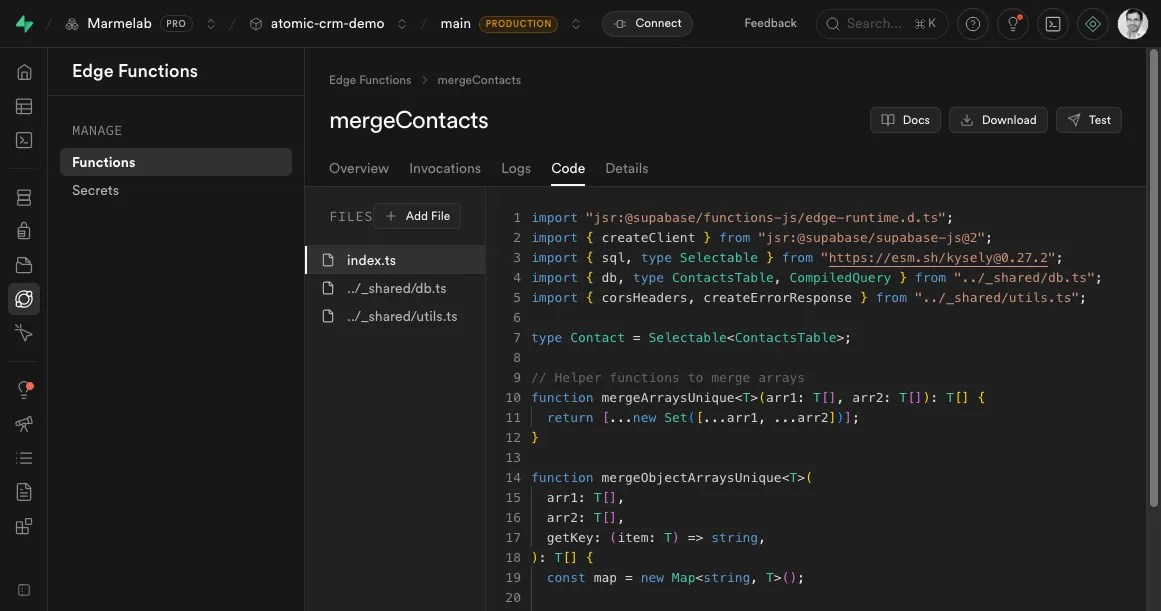
Edge functions are a powerful way to run server-side code close to your users. But how to handle transactions and Row Level Security (RLS) in these functions?

We built a Caddy module to control access to REST resources based on the user's role and a set of permissions.

How to use Google Identity Services as the authentication provider in a React application, a step-by-step tutorial.

This tutorial will show you, step by step, how to configure a React-Admin application to use Azure Active Directory as an authentication provider.

In this post, I will show how to setup the root and user credentials for a Postgres database in a truly secure way, leveraging a secret management system.